Disclaimer: I’m not sponsored by ZeroPointSecurity in any way. This is just my personal review of the Red Team Ops 2 course and exam.
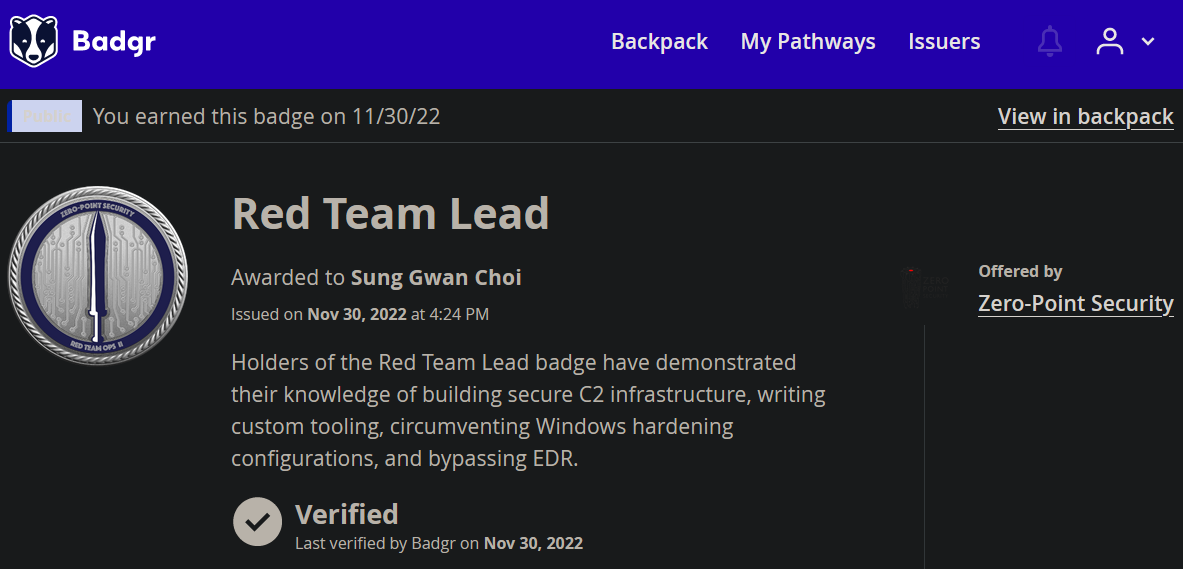
I recently finished the RTO2 course, passed the exam, and received the Certified Red Team Lead (CRTL) certification. RTO2 was a great course that taught me the research side of red teaming. Since I enjoyed the course, the lab, and the exam, I decided to write a review of the course.
Overview

RTO2 is a red teaming course that focuses on "more advanced OPSEC tactics and defense bypass strategies". It is created by Rastamouse from ZeroPointSecurity and is a "continuation" of the RTO1 course which I really enjoyed last year.
If RTO1 focused on the operational side of red teaming, RTO2 focuses on the research side of things. Specifically, these include building red team infrastructure, payload generation with C++/C#, Attack Surface Reduction (ASR) and Windows Defender Application Control (WDAC) bypasses, and defense evasion techniques like syscalls, manual mapping, PPID spoofing, kernel callback neutralization through drivers, and more. For detailed course curriculum, pricing, and FAQ, refer to the official course overview page. Instead, this post will focus on my personal experience and thoughts about the course.
- Course Description: https://training.zeropointsecurity.co.uk/courses/red-team-ops-ii
- FAQ: https://training.zeropointsecurity.co.uk/pages/frequently-asked-questions
Who is RTO2 for?
RTO2 is a course for someone who wants to start their journey in the research side of red teaming. As mentioned in my RTO1 review, there are two sides to red teaming; operation and research. While there may be a small number of red teamers that can only focus on one side, most of the red teams require you to have both skills. Also, most of the infosec folks that I met enjoyed different aspects of hacking; hands-on hacking, creating malw- I mean offensive security tools, and researching new ways of bypassing various defensive controls. Even those who are not that interested in the research side of hacking will often find themselves a need for it to bypass the detective and preventative controls in mature networks.
A One-Stop Shop
However, creating payloads and researching defense evasion are not the easiest things to start learning. There are too many new things that come out every day, in the form of code snippets, blog posts, conference talks, and random tweets.
If you are like me, whenever a big researcher or company drops a blog post, you read it, take good notes, skim through the source code (and understand like 30% of it if it's C/ASM), clone the repo, and fiddle around with it. Maybe try to replicate it or create a small side project that will probably get pushed into yet another private repo. It's kind of difficult to go past that, as you are more of a penetration tester (or a student) and not a professional red teamer that uses these TTP in your everyday work. A couple of days or weeks go by, and you repeat the cycle.
While some are really good at learning things from scattered materials over an irregular amount of time, others prefer a one-stop shop that presents knowledge in a more refined way. RTO2 provides the latter in a clear and concise way. Personally, I "knew" some of the concepts in the courses like PPID Spoofing, System calls, ETW, Manual Mapping, etc. However, my knowledge was very fragmented and I couldn't confidently say that I thoroughly understood the concepts and knew how to implement them. Going through RTO2 helped me to refine my knowledge, implement concepts in various payloads, and test my knowledge in the lab/exam environment.
The Course
Experience with the course material was very similar to RTO1. The materials are straightforward and the instructions are clear and concise. The course material is just enough to the point where it doesn't drown you with too much information, but at the same time, it's not too less information either. There were some modules that I personally thought lacked a bit of information, but there were enough keywords for me to start googling.
The only difference in the experience compared to RTO1 was that I was doing a lot more proactive self-learning using the course material as a reference. RTO1 had the feeling of hand-holding, which was good for a beginner's course. RTO2 on the contrary will lead you down multiple rabbit holes due to the nature of the course. Often I found myself researching, writing payloads, modifying code, reading blog posts, and googling, instead of progressing through the course materials further.
For example, there's a blurb in the course where it tells you "... you can mix and match them (winAPIs) to create your own style of injection". I stopped progressing through the course and spent a couple of days creating a smaller loader that allowed me to choose various WinAPIs that I learned throughout the course. And when learning syscalls, I went back and ported the loader into using SysWhispers3, etc. Just like this, you'll find yourself going down rabbit holes and enjoying the journey.
The Lab
Each machine in the lab is configured with different kinds of defensive controls like a custom EDR, ASR, and WDAC. Overall it serves its purpose and lets you practice the techniques you learn. Unlike RTO1, which the main focus was to operate and compromise the domain, RTO2 focuses on the techniques. So it's not a lab where you start from a machine and "pwn" the domain. It's more of a collection of machines with different kinds of defensive controls like custom EDR, ASR, and WDAC that you can play around with. Some of the machines also have various tools like Sysinternals, process hacker, and API monitorer, so you can observe which kind of traces your TTPs leave.
For infrastructure, RTO2 still uses Snapslab + guacamole combination for the lab. Just like RTO1, Snapslab is great. However, I found myself struggling to code in the lab. So I just used my homelab & dev machine for coding, copy/pasted over the code into the lab machines, and tested them out.
The Exam
Without giving spoilers, here are some of my thoughts regarding the exam. A lot of them are going to be cliché advice and tips because the exam itself was very straightforward.
- You have 72 hours or 5 days (whichever ends first). Plenty of time to work on the exam, don't be stressed about it.
- Just like RTO1, the RTO2 exam tests if you have gone through and understood the course material or not. It's straightforward and most of it is based on the course material.
- Remember that RTO2 is a continuation of RTO1 - all of the techniques and concepts that you learned from RTO1 may apply in RTO2 exam. If you haven't gone through RTO1 but have professional internal pentest or red team experience, brief research on the RTO1 topics in the syllabus should be enough.
- When you are completely stuck and stressed out, turn off the lab and walk away. Take a break, clear your mind, and come back. There's plenty of time.
- All of the tools and techniques that you need to pass the exam are on your testing machine. Use what you got. No need to smuggle through any scripts or tools via base64 + guacamole copy/paste shenanigans. Although, you can use your own payload and tools if you want.
- If you think something is seriously broken, remember Snapslab gives you the ability to reboot and even revert the entire lab. "Have you tried turning it off and on again?"
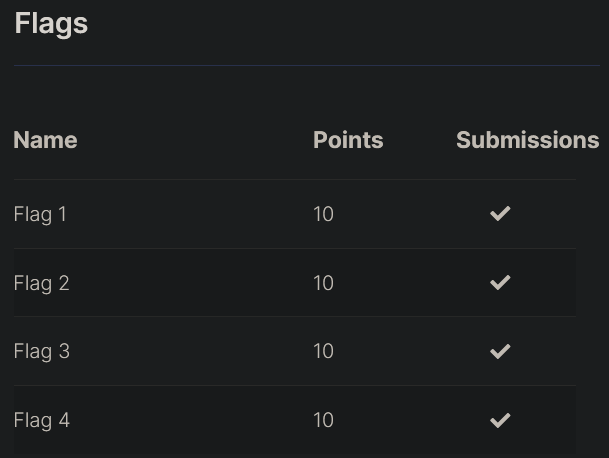
I went through the course material twice on and off for around 5~6 weeks and took the exam. It took me around 17 hours to finish the exam - of which, I used 11 hours for the first flag. I think I've gone through the earth's mantle while going down a couple of rabbit holes. But it was a fun exam and I learned new things along the way.
Conclusion
Overall, RTO2 is a great course to dive deeper into the defensive evasion and the payload generation side of red teaming. Whether you are a professional or a student, the course material will help you in dealing with mature modern networks with various defensive controls.
Happy Hacking!